New OpenSSL Critical Vulnerability: What You Need To Know?
What is OpenSSL?
OpenSSL is a very popular library that’s being used by billions and billions of devices all over the Internet. Basically, it gives you a bunch of cryptographic APIs that allow you to do everything from certificate management, generating certificates, and generating keys to hashing. You can also perform other encryption operations as well. It is a very popular library that is being used from printers to servers that process tons of information in terms of storage and so on. Thus, OpenSSL has become ubiquitous now.
What is the OpenSSL Vulnerability?
OpenSSL is one of the most popular cryptographic software libraries in the world, and it’s used on so many different kinds of machines like E-mail servers, VPNs, web servers, cloud storage, and pretty much anything that is running Linux under the hood which also includes Linux desktops, Mac OS, and FreeBSD. So millions of devices are currently vulnerable to this bug.
October 17th is when there was the initial disclosure of the CVE-2022-3786 and CVE-2022-3602 vulnerabilities in OpenSSL, where it was reported that versions 3.0.0 to 3.0.6 were vulnerable to a flaw. This release is going to include patches for a critical security vulnerability that is currently present within the software.
What are the Vulnerable Versions?
The vulnerabilities (CVE-2022-3602 and CVE-2022-3786) affect OpenSSL version 3.0.0 and later and have been addressed in OpenSSL 3.0.7.
How Severe are these Vulnerabilities?
It immediately brought back memories of the Heartbleed flaw, one of the most famous OpenSSL flaws of 2014 that shook the entire world. But it turned out that it was not as serious as Heartbleed. These vulnerabilities were rated as “critical” when initially disclosed to the public, but later modified to “high” on 1st November. The very fact that the vulnerability has been downgraded from critical to high automatically suggests that it may not be as severe.
How might these vulnerabilities be exploited?
Both vulnerabilities require the following to be successfully exploited:
-
A malicious X.509 certificate that is signed by a valid CA
-
A vulnerable server that parses the client-side TLS certificate
How to Identify and Mitigate Risk?
New applications should be developed to use the latest version of OpenSSL 3.0 (currently 3.0.7). Existing applications using OpenSSL 3.0 should upgrade to 3.0.7 as soon as possible. Existing applications using OpenSSL 1.1.1 are not affected by these issues. However we always recommend using the latest version (1.1.1s). OpenSSL 1.1.1 is supported until 11th September 2023. Users of older versions of OpenSSL (such as 1.0.2) are encouraged to upgrade to OpenSSL 3.0. There was no release of OpenSSL 2.
How ThreatResponder Can Reduce Your Risk?
Cyber security threats, vulnerabilities, and ransomware attacks are increasing at a tremendous pace. It is extremely difficult for cyber security analysts and incident responders to investigate and detect cyber security threats using conventional tools and techniques. NetSecurity’s ThreatResponder, with its cloud-based machine learning threat detection engine and its diverse capabilities, can help your team detect the most advanced cyber threats, including APTs, zero-day vulnerabilities, and ransomware attacks in real-time. It can also help automate incident response and remediation actions across millions of endpoints, making it easy, fast, and hassle-free.
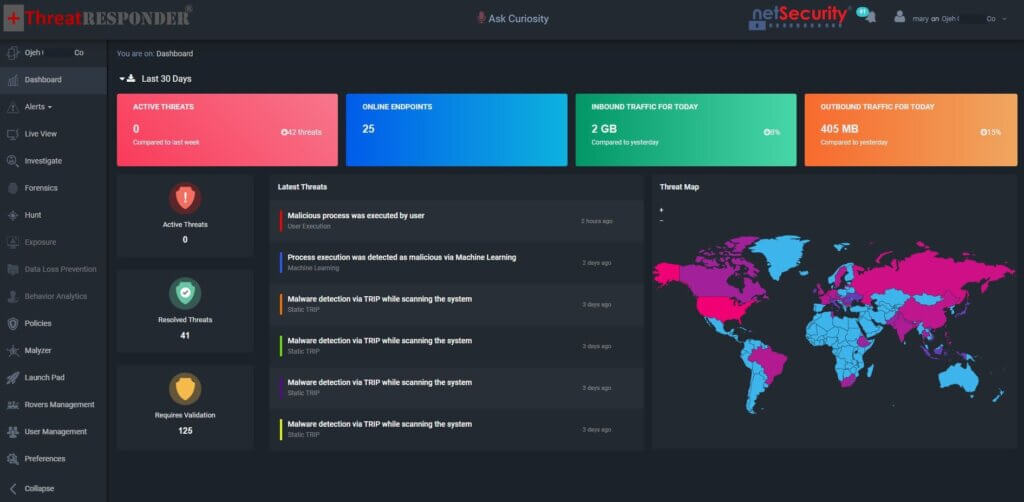
Want to try our ThreatResponder, cutting-edge Endpoint Detection & Response (EDR), and ThreatResponder FORENSICS, the Swiss knife for forensic investigators in action? Click on the below button to request a free demo of our NetSecurity’s ThreatResponder platform.
Disclaimer
The page’s content shall be deemed proprietary and privileged information of NETSECURITY CORPORATION. It shall be noted that NETSECURITY CORPORATION copyrights the contents of this page. Any violation/misuse/unauthorized use of this content “as is” or “modified” shall be considered illegal and subjected to articles and provisions that have been stipulated in the General Data Protection Regulation (GDPR) and Personal Data Protection Law (PDPL).








