Cyber Threat Hunting: An Art of Identifying & Hunting Down Unknown Threats
What is Cyber Threat Hunting in Cyber Security?
Threat hunting is resource-intensive proactive cyber defense activity with a deep understanding of cyber threats and the tactics, techniques, and procedures (TTP). It is a process to proactively and iteratively detect and isolate threats by searching through networks, endpoints, and datasets for any advanced threats or risky activities that evade existing security solutions of criminal adversaries.
Security analysts utilize cyber threat hunting as an active information security technique. It entails exploring networks iteratively for indications of compromise (IoCs), hacker strategies, methods, and procedures (TTP), and threats like Advanced Persistent Threats (APTs) that elude your current security system.
David Bianco’s Pyramid of Pain shows how threat hunting needs to be executed to ensure threat actors can be detected, identified, and isolated before they can disrupt the environment.

Why is Cyber Threat Hunting Important?
This may seem far-fetched, but in reality, attackers can be inside a network for days, weeks, or even months, preparing and executing attacks like advanced persistent threats without any automated defense detecting their presence. Threat hunting thwarts these attacks by looking for covert indicators of compromise (IOCs) that can be mitigated before any attacks succeed. As the volume and complexity of potential threats increases, enterprises are adopting cyber threat hunting functions to improve detection of existing threats and response to cyber threats. Proactive threat hunting detects threats that have evaded perimeter-based security architectures.
Cyber threat detection is different from cyber threat hunting.
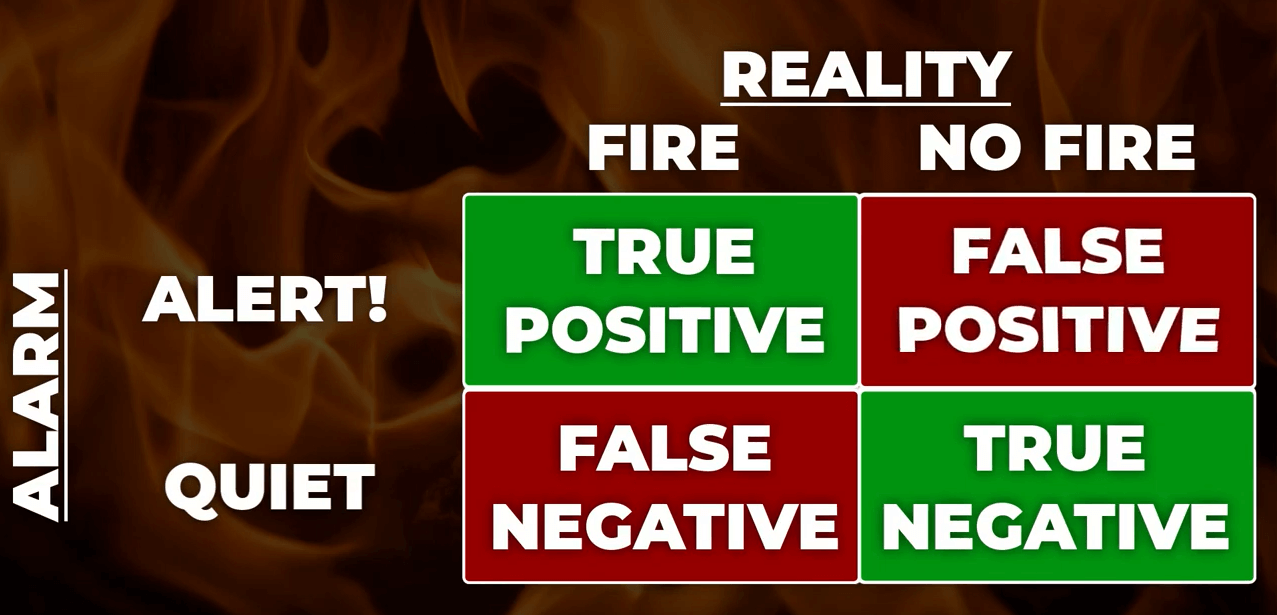
Threat detection is a passive method of monitoring data and systems for potential security issues, but it is still necessary and can support a threat hunter. This is in contrast to traditional threat management measures, such as firewalls, intrusion detection systems (IDS), malware sandbox (computer security), and SIEM systems, which typically involve an investigation of evidence-based data after a warning of a potential threat.
Proactive cyber threat hunting tactics have evolved to classify potential threats ahead of an attack by using new threat intelligence on previously collected data.
Benefits of Cyber Threat Hunting
Threat hunting can dramatically reduce both the meantime to detect (MTTD) and the meantime to respond (MTTR) to threats in half. Threat hunting can help organizations secure their essential assets and reputation by proactively finding security incidents and highlighting threat visibility and coverage holes. SOCs can better utilize their staff and resources by training them in cyber threat hunting procedures. Among them are:
- Data Collections: Cyber threat hunting investigations need to gather a wide range of categories and data from a variety of sources; threat Hunting filters data collection while also increasing the value of security SOC resources.
- Investigation Process: Even the most experienced and well-staffed SOC might be overwhelmed by a seemingly continuous stream of threat alerts and warnings. Swiftly identifying which threats are high, medium, and low risk can reduce threat noise, freeing up security staff time to focus on those that require immediate action or additional study.
- Prevention Process: After a threat has been identified, mitigations must be implemented throughout an organization’s networks, endpoints, and cloud.
- Response Process: Minor, more frequent attacks can be countered with persistent actions, such as removing a tailored script to isolate a compromised endpoint, deleting malicious files after isolation, and automatically restoring data compromised in an attack.
The additional benefits of Threat Hunting are as follows:
- Uncovers Hidden Threats.
- Faster Threat Response.
- Reduces damage and overall risk.
- Helps improve defenses.
- A more efficient approach to identifying threats.
- Reduces Investigation Time.
Cyber Threat Hunting Methodologies
Threat hunting has traditionally always been manual activity in which a security analyst works its way through various data information using their own knowledge and familiarity with the network to develop a hypothesis about potential threats, such as Lateral Movement by Malicious Attackers, but not limited to Threat hunting, but from the other hand, can be partially automated or machine-assisted to make it even more efficient and effective. The analyst leverages machine learning and user and entity behavior analytics (UEBA) software to identify potential threats in this scenario. The analyst then looks into these potential threats, keeping an eye on strange activity in the network. As a result, hunting is an iterative activity, which means it must be repeated in a loop, starting with a hypothesis.
- Analytics-Driven: “Machine-learning and UEBA, used to develop aggregated risk scores that can also serve as hunting hypotheses.”
- Driven by Situational Awareness: “Crown Jewel analysis, enterprise risk assessments, company- or employee-level trends.”
- Intelligence-Driven: “Threat intelligence reports, threat intelligence feeds, malware analysis, vulnerability scans.”
The analyst investigates their idea by sifting through massive amounts of network data. The results are then saved to strengthen the detection system’s automatic portion and serve as a foundation for future hypotheses.
How to Perform Cyber Threat Hunting
According to the Detection Maturity Level (DML) model, threat indicators can be recognized at different semantic levels. Low semantic indications like network artifacts and atomic indicators like IP addresses are more helpful to identify than high semantic indicators like objective and strategy or tactics, techniques, and procedure (TTP). [Requires citation] Typically, SIEM technologies only provide indicators at low semantic levels. As a result, SIEM technologies that can deliver threat indications at higher semantic levels are needed.
- Initial – At this stage of development, Level 0, an organization primarily relies on automated reporting and collects very little data on a regular basis.
- Minimal – Threat intelligence indication searches are included in an organization’s Level 1 maturity. It collects data regularly to a moderate to a high degree.
- Procedural – An organization at Level 2 maturity follows analysis processes provided by others. It collects information regularly at a high or very high level.
- Innovative – An organization at Level 3 maturity develops novel data analysis processes. It collects routine data at a high or very high level.
- Leading – Automates the bulk of successful data analysis activities at Level 4 maturity. It collects regular data at a high or very high level.
Effective threat hunting helps reduce the time from intrusion to discovery, reducing the amount of damage done by attackers. Attackers often lurk for weeks, or even months, before discovery.
ThreatResponder for Automated Threat Hunting
NetSecurity’s ThreatResponder is an advanced cloud-native EDR solution with unconventional capabilities to provide 361° threat visibility of your enterprise assets regardless of their locations. With its diverse features and advanced threat detection and analysis engine, it can help your team identify the loopholes in your organization, monitor the health of the assets, and detect the most advanced cyber threats, including zero-day attacks and ransomware attacks. It can also help automate threat hunting and incident response actions across millions of endpoints, making it easy, fast, and hassle-free. Let NetSecurity’s ThreatResponder EDR increase your cyber security visibility so you can hunt down the potential persistent cyber threats.

Disclaimer
The page’s content shall be deemed proprietary and privileged information of NETSECURITY CORPORATION. It shall be noted that the contents of this page are copyrighted by NETSECURITY CORPORATION. Any violation/misuse/unauthorized use of this content “as is” or “modified” shall be considered illegal subjected to articles and provisions that have been stipulated in the General Data Protection Regulation (GDPR) and Personal Data Protection Law (PDPL).