What is Reconnaissance in Cyber Security?
What is Reconnaissance?
Reconnaissance is a term initially used in military operations to perform preliminary surveys and explore enemy areas by military personnel to gather enemy information. Reconnaissance in cyber security is a process of gathering information about the target organization. For an attacker, the first step of hacking involves collecting crucial information regarding the target so the attacker can then utilize this information to exploit and penetrate the target networks. Attackers can covertly gain critical and confidential information by using different recon techniques without engaging with the target network.
Types of Reconnaissance
There are two main types of Reconnaissance employed by hackers in cybersecurity. They are:
Active Reconnaissance
Active Reconnaissance, which cybercriminals use to gather information about computer systems, uses tools like scanning, manual testing, ping, and netcat. Active Reconnaissance is faster and more accurate because it generates more noise within the system and has a higher chance of detection.
Passive Reconnaissance
In passive Reconnaissance, attackers can gather data without interacting with the application or framework we are trying to understand. This is accomplished by conducting web searches and downloading free reports. IP addresses are not traced through passive Reconnaissance. The target can be reconned passively without having to interact with it. This means that the target does not receive a request and is unaware that passive recon is being conducted. In most cases, passive information gathering involves accessing public resources that contain information about a target.
Different Sources of Information For Reconnaissance
During reconnaissance work, the following sources of information are often used:
- Domains and subdomains
- Whois Information
- Directory info
- Amazon S3 Buckets
- Social media accounts (individuals and the company itself)
- Dark web breached accounts for the domains in question
- Calling individuals in the company to Social Engineer information about the company out of them
Different Reconnaissance Techniques
According to Mitre, the following are the most common reconnaissance techniques that attackers use for gathering information about the victim.

- Active Scanning [T1595]
- Gathering Victim Host Information [T1592]
- Gathering Victim Identity Information [T1589]
- Gathering Victim Network Information [T1590]
- Gathering Victim Organization Information [T1591]
- Phishing for Information [T1598]
- Search Closed Sources [T1597]
- Search Open Technical Databases [1596]
- Search Open Websites/Domains [T1593]
- Search Victim-Owned Websites [T1594]
Different Reconnaissance Tools
Following are some of the essential tools that help perform reconnaissance activities:
- Nmap
- Metasploit
- Wireshark
- Shodan
- Nessus
- OpenVAS
- Maltego
- Dmitry
- Hawkscan
- Traceroute NG
- Nslookup
- Recon-ng
- Aircrack-ng
How to Detect Reconnaissance Attempts?
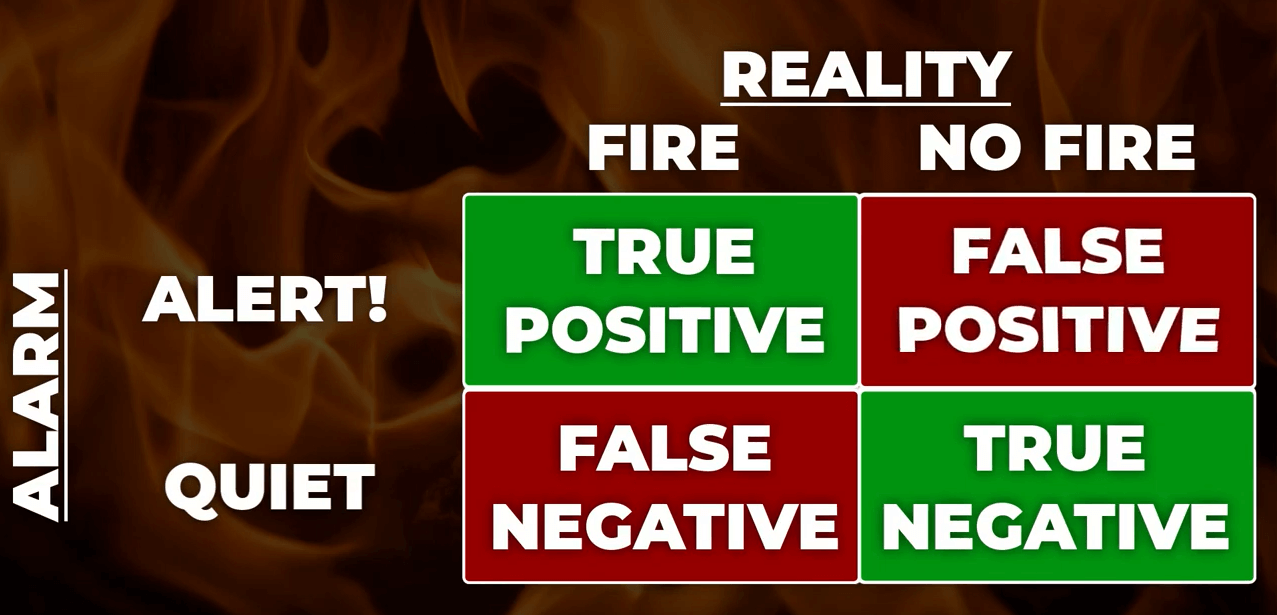
Reconnaissance is critical for an attacker to exploit any target organization. Detecting passive Reconnaissance is impossible since it does not involve any active engagement with the target network. However, active reconnaissance attempts can be identified using advanced tools and techniques. Detecting an intrusion at the reconnaissance stage can avoid significant damage to the organization. Recon activities are detected mainly by the network security tools like Network Firewalls, Switches, Intrusion Detection Systems (IDS), and Intrusion Prevention Systems (IPS). These network security systems can effectively alert any abnormal activities detected in the network traffic. Any random inbound traffic seeking suspicious information can be flagged as a recon activity.
How To Improve Your Enterprise Security Posture To Detect Recon Attacks?
Cyber security threats are rapidly increasing at a tremendous pace. It is extremely difficult for cyber security analysts and incident responders to investigate and detect threats using conventional tools and techniques. NetSecurity’s ThreatResponder, with its diverse capabilities, can help your team detect the most advanced cyber threats, including APTs, zero-day attacks, and ransomware attacks at different stages of the cyber kill chain. It can also help automate incident response actions across millions of endpoints, making it easy, fast, and hassle-free.

Disclaimer
The page’s content shall be deemed proprietary and privileged information of NETSECURITY CORPORATION. It shall be noted that NETSECURITY CORPORATION copyrights the contents of this page. Any violation/misuse/unauthorized use of this content “as is” or “modified” shall be considered illegal and subjected to articles and provisions that have been stipulated in the General Data Protection Regulation (GDPR) and Personal Data Protection Law (PDPL).