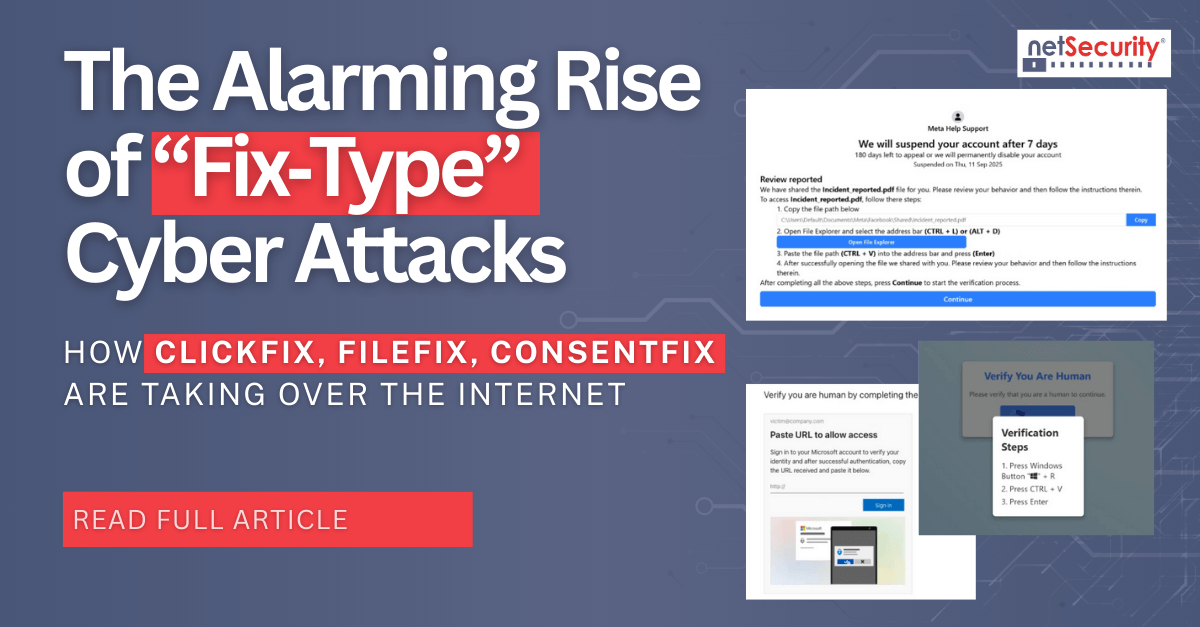
The Alarming Rise of “Fix‑Type” Cyber Attacks: How ClickFix, FileFix, ConsentFix Are Taking Over the Internet
Fix‑type attacks are a family of social engineering techniques that coerce users to copy, paste, and execute attacker‑supplied content under the guise of fixing an error or proving they are human. The hallmark is a browser interaction that silently or explicitly places code or key material on the clipboard, then instructs the user to execute it in a trusted local context. Recent variants include ClickFix, FileFix, and ConsentFix, and they...